Why traditional ITOps is failing to keep up with the unique nature of AI incidents
If 2025 was the year of AI adoption, with 88% of organizations now using AI across at least one business The post Why traditional ITOps is failing to...
If 2025 was the year of AI adoption, with 88% of organizations now using AI across at least one business The post Why traditional ITOps is failing to...
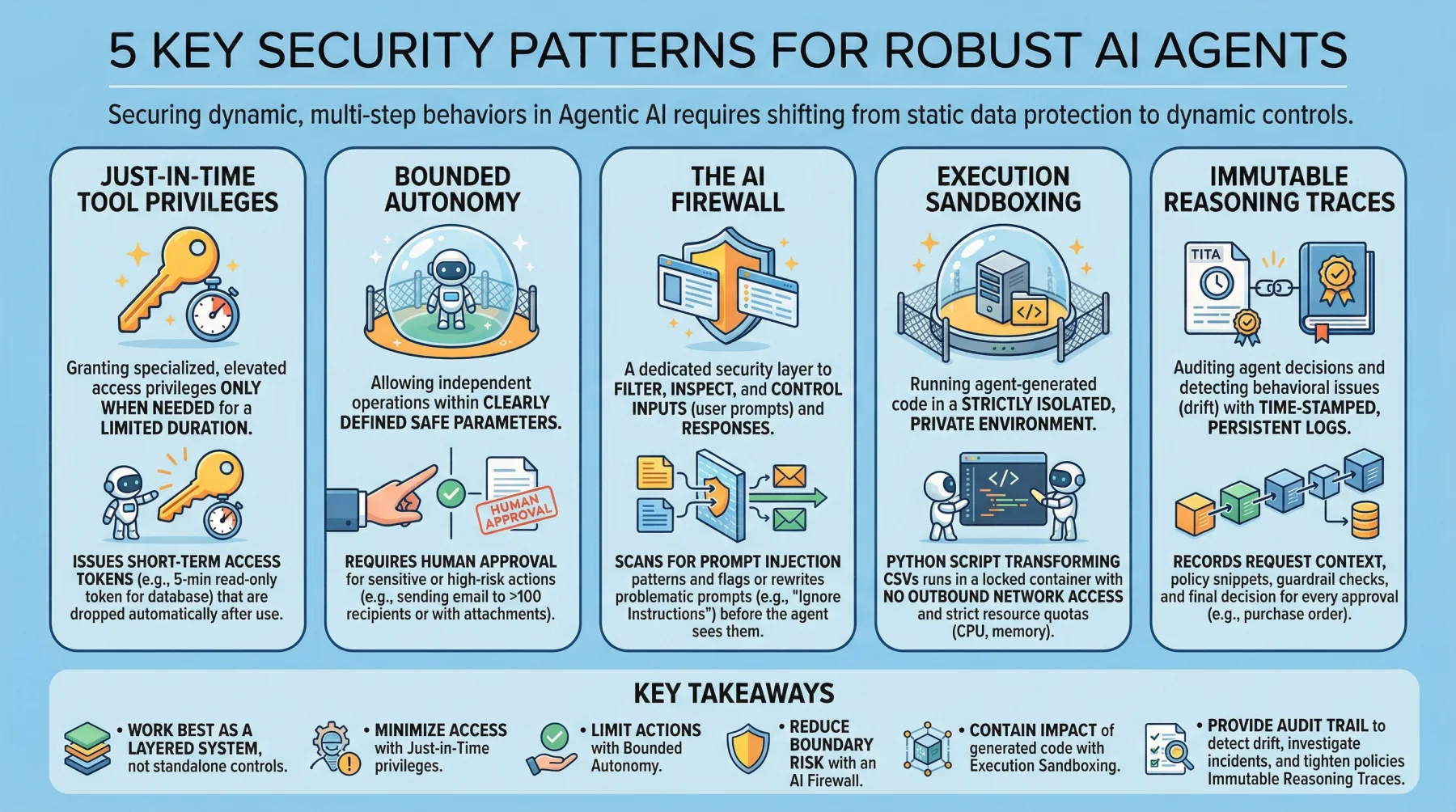
5 Essential Security Patterns for Robust Agentic AI By Iván Palomares Carrascosa on March 5, 2026 in Artificial Intelligence Share Post Share 5 Essent...

Valentyn Pavliuchenko, head of Hosanna Studio, suggests replacing inhumane AI prompting with intuitive, high-performance interfaces that bridge the ga...

The Eclipse Foundation this week announced that Open VSX, the open source extension registry for tools built on the VS The post Eclipse Foundation rep...
This article introduces and explores Kedro's main features, guiding you through its core concepts for a better understanding before diving deeper into...

While traditional penetration testing relies on manual or point-in-time assessments, often delivered weeks after software has already shipped, softwar...
OpenAI has released GPT-5.3 Instant, the latest iteration of the fast, general-purpose model that powers everyday interactions in ChatGPT. Rather than...

Four years is a long time in technology. But in AI, it’s more like an eternity. When Unleash last raised The post Unleash raises $35M, launches...

How Martin Kleppmann’s iconic book is evolving for AI and cloud-native architectures Since its release in 2017, Designing Data-Intensive Applica...
Spending hours cleaning, summarizing, and visualizing your data manually? Automate your exploratory data analysis workflow with these 5 ready-to-use P...

The integration of WebAssembly (Wasm) into the Helm ecosystem streamlines the orchestration of WASI-compliant binaries across disparate environments,...
There will come a time when you need to not only back up your data, but also create an image The post How to clone a drive to an image with Clonezilla...

Internal access management (IAM) is seeing compounded growth in demand and adoption as a key component in zero trust and The post Why 83% of organizat...
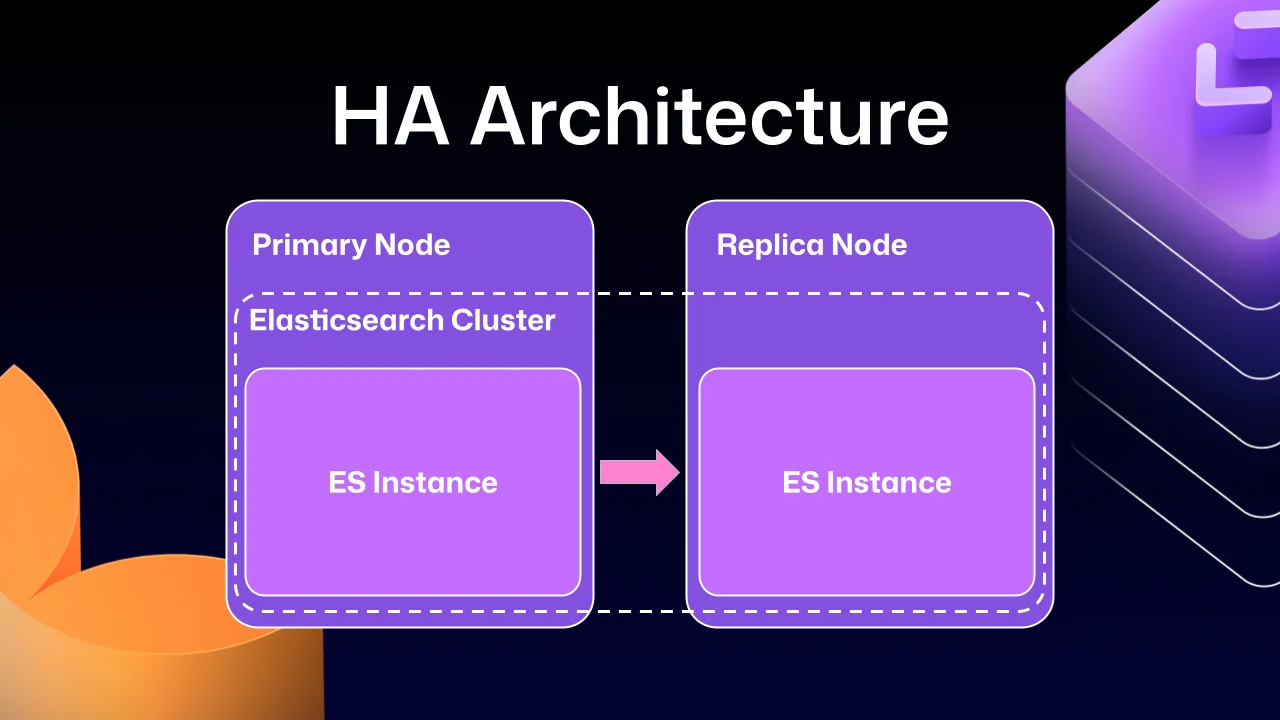
Here's how we the search experience better, faster, and more resilient for GHES customers. The post How we rebuilt the search architecture for high av...
Confluent recently unveiled support for the Agent2Agent (A2A) protocol, an open standard for inter-agent communication. The platform’s implement...

Skills are what make OpenClaw more than a local assistant, and these are the most popular ones worth installing today.

OpenClaw is in the ascension. This open source autonomous AI agent has this year surpassed Linux on the GitHub all-time The post OpenClaw rocks to Git...

In Barcelona this week, a bit of tension is in the air for certain attendees at the annual Mobile World The post Developers are coding to a moving tar...
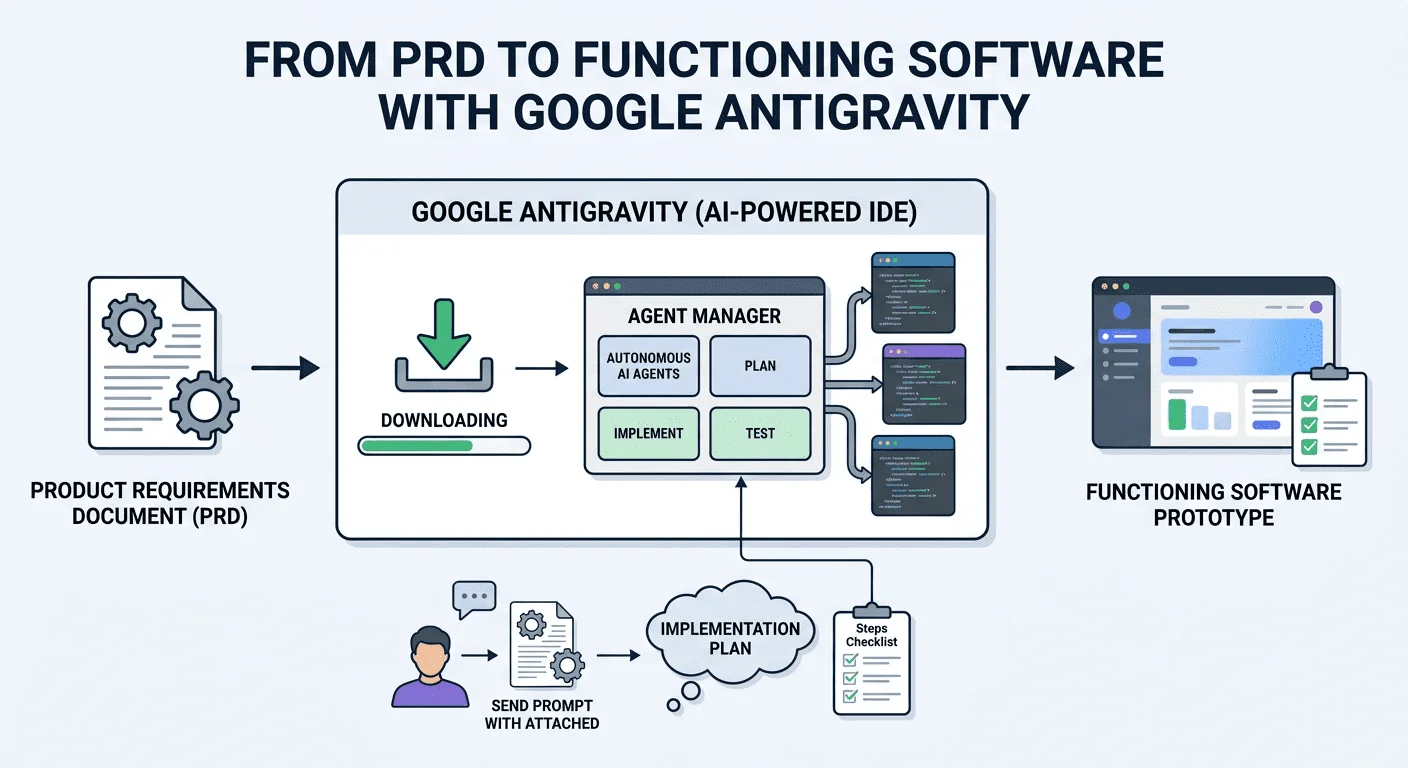
This article guide you through an example use case to turn a PRD into a functioning software prototype using Google Antigravity.
An AI agent combines a large language model for reasoning, access to tools or APIs for action, memory to retain context and a control loop to decide w...